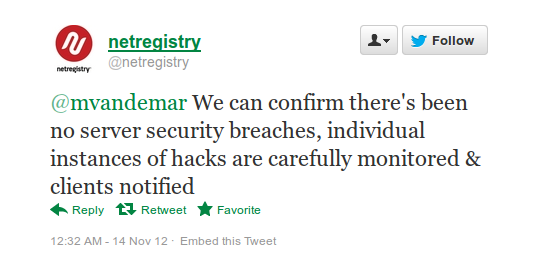
It looks like another pair of hosts have joined GoDaddy in the “Not our fault” game when their servers get breached. Yesterday I had a few people contact me whose sites had been hacked, all with the identical symptoms: the only thing showing on their sites are the words hacked by hacker in plain text, on a white background. The one thing they all had in common is that they were hosting with either HostPapa or Netregistry, and the one thing that both hosts had in common is that they refused to own up to the problem:
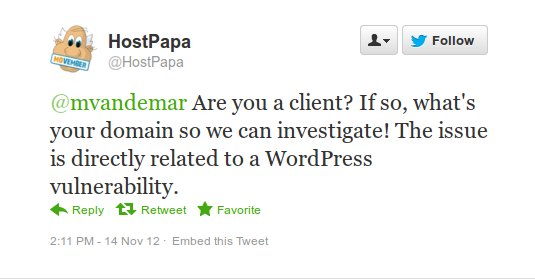
and in HostPapa’s case they are even trying to blame it on WordPress:
Isn’t it nice the way they are able to determine that it is a WordPress issue, without even knowing which site it is? These styles of hacks, which usually have a specific hacker’s tag or signature rather than just “hacker”, often indicate to me that something other than a standard scripting exploit is at play. Whenever I see a site hit with a similar defacing hack, the first thing I do is check to see if there are other sites affected on the same host.
Warning: I am on Linux, which is unaffected by viruses that can affect Windows users. Unless you are on Linux or a Mac you should exercise extreme caution when looking for hacked sites, even if you have up to date antivirus software installed.
The way I check is I ping the infected domain in order to get the IP address, which in this case was srv03.netregistry.net (180.235.128.204), which I then plug into Bing using their “ip:” advanced search option (search by IP), plus the phrase “powered by WordPress”:
http://www.bing.com/search?q=ip%3A180.235.128.204+%2B%22powered+by+Wordpress%22
Clicking through those results I could easily see that this was far from isolated, and by using Bing’s cache I was able to determine that many of these sites were in fact up to date running the latest WordPress version before getting hit. I then tried several other of their servers (srv01.netregistry.net, srv02.netregistry.net, and srv04.netregistry.net), all with the same result. I sent them a tweet letting them know that they appeared to have an issue, and they replied, as shown in the screenshot above, that they were able to “confirm there’s been no server security breaches”. I then gave them examples of 15 identical hacks across 4 different servers of theirs here, here, here, and here. As of yet they have not bothered to reply to those tweets.
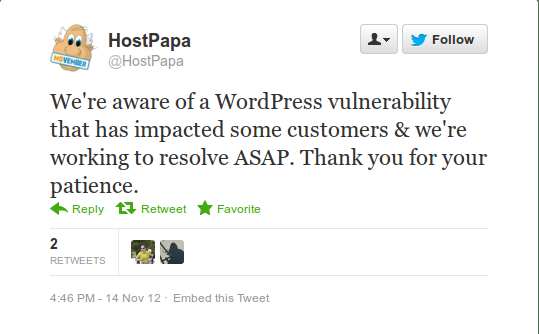
While I was in the midst of investigating Netregistry, someone else contacted me with the exact same hack, only their site was hosted with HostPapa. Going through the same process (as well as checking with recent forum posts from people with these symptoms) I checked hp82.hostpapa.com (76.74.128.200), hp78.hostpapa.com (76.74.128.160), and hp86.hostpapa.com (76.74.242.140), and found the same issues with all of them. Regardless of the evidence, however, HostPapa is still insisting that this is a WordPress issue:
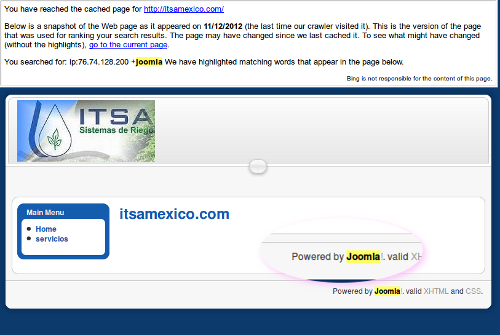
There are a few issues with them trying to blame this on WordPress. First off, if this were an issue affecting WordPress installations that were up to date with the latest (which is 3.4.2, which quite a few of these sites were running), then it would be much, much more widespread, and it would not be isolated to just these two hosts. Secondly, if this were a WordPress issue then why was I able to find at least 1 Joomla site on HostPapa with the exact same hack?
I let HostPapa know this via a tweet, but they were uninterested in addressing that. Instead they seem more intent on blaming it on WordPress, telling their clients that they don’t help with hacking issues, and pretending that everything is fine. Just because a slew of sites that get hacked on a server are all running WordPress does not make it a WordPress issue. WordPress is a database driven platform, and is the most popular one out there. If a hacker locates a MySQL based exploit on a given host then the fastest ways to find a large number of sites to target would be to do searches similar to the ones I did above and aim for the WordPress ones. I am guessing this is actually what happened here, and it is obvious that this isn’t some 0-Day WordPress exploit (like both HostPapa and this idiot here are trying to claim).
Regardless of whether or not they eventually own up to it, if you are one of the unfortunates who happens to be hosting with either of these companies I would highly recommend you switch hosting, even if you are not one of the ones that got hacked. Again, I always recommend Hostgator, both for their security and for the fact that they happen to have better performing servers than many of the other hosts out there.
If you did get hit and you just want to get back up and running as fast as possible, luckily with the instances I saw this isn’t actually too difficult. While the next wave of hackers who come through might do more damage, at this point it seems to simply be a matter of replacing your root index.php with a fresh one from a clean WordPress install, and replacing either your index.php or header.php (or both) inside your theme using backups or clean downloads (assuming you have a readily downloadable copy of the theme you are using). I also saw some instances of people being unable to log in to the WordPress admin interface. The solution to that, as I described here, is to go in to your database through the phpmyadmin in cpanel and look at the wp_users table. If they switched the admin username and email, edit the record to switch it back and then go through the Lost Password function on the WP login page.
One thing to be careful of is that often times in cases like these the hackers will drop back doors on the sites, so that even once the host fixes the initial issue the hackers can just get right back in again later. If anyone has any issues where they keep getting hacked, even after moving to a new host, I am available to do professional cleanings. Feel free to contact me for more information. Also, Hostgator does offer free migrations in some instances, but if you have multiple or complex sites that you would like migrated to them I can assist with that as well (or to another host if you prefer, of course).
More resources:
How To Clean Hacked WordPress
WordPress FAQ: My site was hacked
How to find a backdoor in a hacked WordPress