 Getting hacked sucks, plain and simple. It can affect your rankings, cause your readership to be exposed to virus and trojan attacks, make you an unwilling promoter to subject material you may not actually endorse, and in many cases cause the loss of valuable content. However, once it happens it is usually best to not procrastinate on the clean up process, since a speedy restore will most times minimize the damage that was caused.
Getting hacked sucks, plain and simple. It can affect your rankings, cause your readership to be exposed to virus and trojan attacks, make you an unwilling promoter to subject material you may not actually endorse, and in many cases cause the loss of valuable content. However, once it happens it is usually best to not procrastinate on the clean up process, since a speedy restore will most times minimize the damage that was caused.
While almost all sources will recommend that you upgrade your WordPress to the latest version, what the majority neglect to tell you is that in most cases simply doing so will not prevent the attackers from getting back in, even if there are no known exploits with the latest version. The hackers may have left a back door file hidden in a directory where it wouldn’t get overwritten with an upgrade, or inserted code into your theme, or simply created an account that they then granted admin privileges to. Any one of those would allow them back in, even after you patched what was wrong the first time. Therefore I am providing this step by step process on how to completely clean out and restore a WordPress installation that has been hacked.
1. Backup the site and the database.
Even a hacked copy of your blog still probably contains valuable information and files. You don’t want to lose this data if something goes wrong with the cleanup process. Worst case scenario you can just restore things back to their hacked state and start over.
2. Make a copy of any uploaded files, such as images, that are referenced.
Images are generally exempt from posing a security risk, and ones that you uploaded yourself (as opposed to ones included with a theme, for instance) will be harder to track down and replace after things are fixed again. Therefore it is usually a good idea to grab a copy of all the images in your upload folder so as to avoid broken images in posts later. If you have any non-image files that could potentially have been compromised, such as zip files, plugins, or php scripts that you were offering people, then it is a good idea to grab fresh copies of those from the original source.
3. Download a fresh version of WP, all of the plugins you need, and a clean template.
Using the WordPress automatic upgrade plugin does make it easier to upgrade every time a new version comes out. However, it only replaces WordPress specific files, and does not delete obsolete ones. It also leaves your current themes and plugins in place, as is. This means that if used to upgrade a blog that has already been compromised, it can very well leave the attackers a way back in. It is best to start over from scratch as far as the files portion of your installation goes. Note that if you use the EasyWP WordPress Installer script that I wrote it saves you from having to download, unzip, and then upload all of the core WordPress files, although you will still need to grab fresh copies of the themes and plugins that you want to use.
4. Delete all of the files and folders in the WP directory, either through FTP (slower) or through cPanel’s File Manager (faster).
Now that you have fresh copies of all the files you need, and copied all of your uploaded images, completely delete the entire directory structure your blog is in. This is the only surefire way to completely remove all possibly infected files. You can do this through FTP, but due to the way that FTP handles folder deletion (ie. it walks the directory structure, stores each and every file name that needs to be deleted, and then sends a delete command for each one), this can be slow and in some instances cause you to get disconnected due to flooding the server with FTP commands. If available it is much faster to do this through either cPanel’s File Manager, or via command line if you happen to have shell access.
5. Re-upload the new fresh copies you just grabbed.
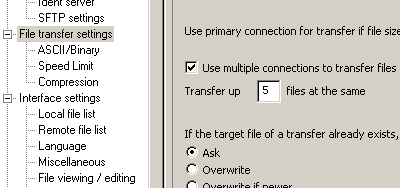
This step should be self explanatory, but I would like to mention that if your FTP client supports it (I use FileZilla, which does) and your host allows it, then increasing the number of simultaneous connections you use to upload can greatly reduce your overall transfer time, especially on servers or ISP’s where latency is more of an issue than bandwidth. In FileZilla this setting is found by going to “Edit -> Settings -> File transfer settings”:
Also, if not using the EasyWP WordPress Installer script, don’t forget to edit and rename your wp-config.php file (when freshly unzipped this is named wp-config-sample.php).
6. Run the database upgrade (point your browser at /wp-admin/upgrade.php).
This will make any necessary changes to your database structure to support the newest version of WordPress.
7. Immediately change your admin password.
If you have more than one admin (meaning any user with editing capabilities), and cannot get the others to change their passwords right then, I would change their user levels until they can change their passwords as well. If there is anyone in your user list that has editing capabilities, and you do not recognize them, it’s probably best to just delete them altogether. If changing passwords is something you hate doing, then maybe my new memorable password generator can make that a little less stressful for you. 😀
8. Go through the posts and repair any damage in the posts themselves.
Delete any links or iframes that were inserted, and restore any lost content. Google and Yahoo’s caches are often a good source of what used to be there if anything got overwritten. The following query run against the database can help you isolate which posts you want to look at:
SELECT * FROM wp_posts WHERE post_content LIKE '%<iframe%' UNION SELECT * FROM wp_posts WHERE post_content LIKE '%<noscript%' UNION SELECT * FROM wp_posts WHERE post_content LIKE '%display:%'
If you did not change the default prefix for WordPress tables, than you can copy and paste that directly into a query window and run it, and it should pull up any posts that have been modified to hide content using any of the methods I have come across so far (iframes, noscript tags, and display:none style attributes). To get to a query window in cPanel, you would click on the MySQL® Databases icon, scroll to the bottom of the page, and then click on phpMyAdmin. Once the new window or tab opens, you would click on the database in the left hand side that your blog was in, and then in the right side at the top click on the SQL tab. Then just paste the query into the large text area and hit the Go button.
Note, however, that there may be other types of injected content that I haven’t seen yet, and that a manual inspection looking for the types of patterns that first alerted you to the fact that your blog was hacked is always a good idea.
UPDATE: 9. (still valid in 2015) If you are having issues cleaning the installation yourself
When I wrote this post back in 2008 I intended it to be a do it yourself guide for the non-techie. However, I do realize that some people would still rather a professional programmer perform many of the steps I outlined here. If anyone has had their WordPress installation hacked, and either is uncomfortable attempting to clean it on their own, or has tried to do so with no success, I am available on a case by case basis. Most cleanings can be performed in about one hour, two at the most. The time can vary depending on the size of the blog, the amount of customization to the original theme, and the number of plugins installed. Feel free to contact me here if you feel like you could benefit from my help. Please include the site and any details that you think might be relevant (pro theme, anything you may have tried on your own, etc.) in the contact form.
UPDATE #2: 10. A note on hosting.
This past year (2010) has seen multiple waves of attacks on people’s websites that happened not due to insecurities within the WordPress platform itself, as has historically been the issue, but rather due to vulnerabilities with the actual hosts. Some of the bigger names that were hit include GoDaddy, Rackspace Cloud, MediaTemple, and Network Solutions, for instance. It is very important that you use a host that is not only well versed in security, but one that is stable and has knowledgeable tech support as well.
Update #3 11/14/2012:
Please note: if you are currently hosting with either HostPapa or Netregistry and you are here because you were hacked then the following tutorial may not be sufficient. Please see this post for more details:Hosting with HostPapa or Netregistry and Hacked? Switch Hosts Now. (hacked by hacker)
My personal recommendation for shared hosting is Hostgator. It is where this blog and many other sites of mine are currently hosted. Yes, that is an aff. link, but I would recommend them even if it wasn’t. For a dedicated solution that is both affordable and robust I use The Planet, which is where I host Bad Neighborhood. Both companies are ones that I have been using for years without issues, and that I do recommend to my own clients when they find themselves dissatisfied with their current hosts. If you were hacked, and your WordPress was up to date when it happened, then a change of hosts is something you should consider looking into.
Very nice post bro, I hope you could have posted it lill before to help me out of this situation… lol
Anyhow, I am sure it will be very helpful to some else who is stucked in such situation. Thanks for the useful post
Image files can be used to carry both hidden information and executable code (malware). While I agree the risk is not great, you should be careful about everything you port forward from a hacked installation to a new installation, including images. If you have pre-hack copies, certainly use those instead. Also, the existence of many images you did not put up yourself may be evidence of the intent of the hacker. Your site may have been intended to be used as a distribution point or hub… and you should ask your host to help make sure the new setup is protected against that sort of abuse.
Actually, no, you cannot infect someone with a virus or other malware through an image. At worst a hacked blog might have their images defaced or destroyed, but that doesn’t actually pose a danger to the readers.
Excellent post. Definitely worth my Digg.
There is one thing I would add to the list – use a vulnerability scanner on a regular basis.
Spend $50 a month and have someone scan your site every day so you know when is the next time you are vulnerable. I just thought about how much this hack had cost me including downtime when I make no sales, loosing customers and reputation, and the cost of recovery, assuming I have an updated backup…
It is definately helpful to know how to recover but it is more important to make sure you are not falling again.
Great post! Unfortunately most folks don’t heed the advice to prepare and backup until something happens to them. Just like backing up a hard drive. But once it happens, they realize how important it is and never forget. It’s good to have the peace of mind that you have a plan in place to deal with something like this when it happens. I recommend printing up the post and keeping it as a Standard Operating Procedure for dealing with the possibility of being hacked.
Sounds like Atlaf just went through the same thing..I’m sure he’ll be prepared if it happens again thanks to your informative post. Keep up the good work! Enjoyable and informative blog on what can sometimes be a boring subject.
You might be getting hundreds of “thank you”s by the end of the year with this post. Thanks for laying out everything step by step. I have dozens of people forward this post to 🙂
@Michael VanDeMar there have been malware vectors abusing images files since 2002, and stegonographic manipulations since before that.
You misread me – I never said you would get a virus from the image. I said the image can carry malware – payload code, which can be executed if you have any of several existing Windows viruses on your system. Search perrun for an example.
In this context it was said that you can safely keep your images after you’ve been hacked. My caution was that they may have been modified, so if you have your originals, you are better off resoring them because images are not 100% “safe”. It is not best-practice to retain anything after a hack if you have other options.
Just say “wush wush go away hacker!” and there they fly away 🙂 No sorry, it is a pain in the ass, you should always have the last version and a managed server that is up to date, for my situation that would be sufficient. good luck! Aislin
Actually, Hypotheek, one of the reasons they keep coming out with new versions is because the older ones have security holes in them. Just having the latest version is never a guarantee that it is safe. The most you can say is that having an older version is pretty much a guarantee that you are not safe.
Great info, who knows it might be coming handy one day (hopefully not)
Another way to prevent security loophole in WP or any other PHP based CMS is to tighten the security at the server level.
Thats great info. I’ll try to run those SQL in my wp sites now and check them.
Thanks for the tips 🙂
Good info. Does anyone have some great plugin or tool to backup your WP a little faster?
Thanks, Kopen
I have had to deal with four or five wp hacks in the past year, so this post helps alot. Sometimes I dont know where to start.
Great post! i had a lot of hackproblems the past couple of years so this would help me a lot.
This is really good to mentione! Most of the times this advice is for many too late. Thank you for sharing. Greetz, Jasper
Wow, great reference article, worked great right away.
I’m going to do all this, thanks.
But while preparing all this, I at least cleaned my unauthorized admins out of my db with a few queries: http://spacefem.livejournal.com/555475.html
Thanks for this great article. I’ve had to deal with three wordpress-hacks this year, so this post helps me a lot!
I have been hacked and just found out. I know it was my fault as I did not update because of problems my daughter had when she updated, and I felt like things were going fine for me so did not do it.
I am sorry now, but also confused as to what to do. I am not as young as many of you, and so sometimes things scare me a bit!
I exported my XML that wordpress makes for you as well as all my images, but now do not know what I should do. I also forget how to install wordpress from the beginning which is what I think I need to do now, wipe out all the old and then put in a new, right?
Then, is it not safe to just import my old posts? I hate to lose everything, but do I need to start over and let the two or 3 years of posts get dumped?
UGH, I am upset.
Hey
My site just went down in a way that has never happened before. I was not working on it either plus I had done some major marketing. It was a strange coincidence that I had emailed someone who deals with security, just before it happened and obviously competitors may have done it.
The site is http://www.csv2post.com now I was not too bothered to be honest its very new, not a lot of traffic but I’m dead certain it was a hack, even hosting thinks it was.
Anyone good at hacking want to offer a fee to fix the issue or are these hacker plugins around working enough and giving enough security to not bother paying?
Ryan
Thank you Michael for all these useful details. Unfortunately, most of people become wise just after a hacker attack… The main rule remain a constantly backup of your databases.
By upgrading your blog to the last version – and for the plugins also – it`s a way to keep away the common hackers attacks; but don`t forget, never you can`t be sure, this is the nature of the web and only with an early backup you keep in sure the most of your important dates.
I cant thank you enough for helping me rescue several of my wordpress sites that were hacked.
Once again thanks
I have a photography blog at http://shoots.wedding-photography-melbourne.com.au – I have just recovered from a hack that went deep into the database. I had to export my posts as an xml file from the hacked WordPress site and import that file into a new, freshly created database… Arrgh. New passwords, redownload of the plugins and template files – absolutely everything new and clean. The call across the board is to stay current with your WordPress installation and you’ll have less chance of problems.